MMD is a cloud-based service that brings together M365 Enterprise and adding these features.
- End-user device deployment
- IT service management and operations
- Security monitoring and response
- End-user support.
Current challenges for business and people:
- The transition to the agile world of software as a service is daunting.
- End users want an empowered, connected work experience.
- Many current IT management and security processes are outdated, time-intensive, and expensive.
- Businesses want to focus on what makes them uniquely successful, rather than maintaining digital infrastructure.
Your end users will enjoy the latest versions of Windows 10 and Microsoft 365 Apps for enterprise apps (and more besides), using devices and software that are curated and rigorously tested for best performance and reliability. Also, you'll never have to worry about keeping any of this software up to date because that happens automatically, following a careful rollout sequence that is monitored every step of the way. And registered devices are monitored 24x7 for technical and security issues, so if something goes wrong, help will be on the way.
Unique to Microsoft Managed Desktop
MMD policies and security baseline offers end users these benefits:
- Boot times for MMD devices about 1/4 as long.
- At least twice the battery life.
- About 1/3 as many device crashes per year.
- Device mobility through Enterprise State Roaming, allowing users to have teh same experience no matter what device to sign into.
IT admin benefit from these features:
- Insights dashboards constantly keeping you up to date on usage, reliability, device health, and other data on devices and users.
- About 1/10 the amount of time needed to update 95% of devices.
- More time to focus on other IT admin activities, thanks to device management provided by the service.
- Better awareness of device and app performance and early warning of security issues from device monitoring.
Device management:
- Hardware
- Instead of your IT department having to research and test devices (and their drivers), specific devices are carefully tested by MMD, resulting in a curated list of devices that meet enterprise-level performance requirements and are guaranteed to work with the service. You can either obtain devices yourself (or work with a partner) or reuse devices you already have, provided they are on the approved list. Registering devices is easy and straightforward, and before they're deployed, you can also customize certain aspects of the device experience for your end users.
- Updates
- MMD sets up and manages all aspects of deployment groups for Windows 10 quality and feature updates, drivers, firmware, anti-virus definitions, and Office ProPlus updates. This includes extensive testing and verification of all updates, assuring that registered devices are always up to date and minimizing disruptions, freeing your IT department from that ongoing task.
- Apps
- As part of Microsoft 365 Enterprise, Microsoft provides (and manages) several key Microsoft apps for you. But you probably also have other apps that you need for your business. Instead of your IT department having to test, package, and deploy those apps Microsoft helps you deploy them and can assist with Desktop App Assure if needed. Learn more at Apps in MMD.
Device monitoring
- help maintain the security of your devices with a dedicated security operations center that monitors your devices and uses data from the unique threats that Microsoft analyzes each month. These security features are built in instead of added on later. Also monitor device health and provide you with insights about device performance
Product Lifecycle:
- Product Release and evaluation
- Product's first 6 months after GA
- evaluates things like reliability and performance, compliance with a hardware baseline, market sentiment, and inventory and channel readiness, among other things. (It takes about 6 weeks to complete)
- Output: Product certification is done, Product is added to the approved product list.
- Product Primary Availability Period
- Two years of "open enrollment" period. Device enrolled during this period will receive 3 full years of support. The device will be added into device list. and finally it will be moved to archived device list.
- Product Grace Period
- a three-year period following primary availability.
- Product Retirement
- no new devices of that product type can be enrolled
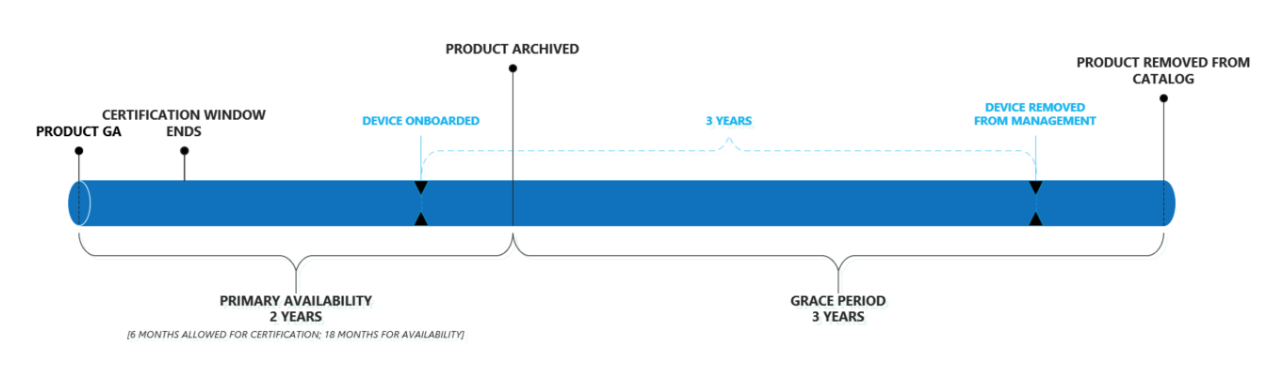
每个产品有三个重要日期:1) Approved Date->Product's GA Date 2) End of the primary availability Date 3) End of eligibility Date
Products remain on the catalog for up to 24 months, but devices remain under management for 3 years based on their individual enrollment dates. 所以上面的日期都是可以根据Approved Date计算出来,从而公司IT部门可以相应的提前做计划。
Device currently Supported by MMD are products from Dell, HP & Surface. They should meet or exceed the listed specifications for RAM, processor family, and disk space.
Device Service including:
- Support: Support agents will answer questions directly related to device functionality and diagnose device issues.
- Inventory: All devices are tracked in the MMD Admin portal for inventory and status tracking.
- Firmware/Driver updates: By default, MMD devices receive firmware and driver updates from Windows Update. Not all hardware partners deploy their updates via Windows Update. Updates not published as Automatic require an exception and must be deployed by the customer.
- Accessories: Accessories that come with your device are covered by the same services as the device itself, but warranty terms may differ. Refer to the warranty terms chosen when selecting your devices.
- Device Setup: Devices will be pre-configured with the current version of Windows and receive their apps and configurations via the cloud.
Device Service limitation: It doesn't support:
- Personalization: Devices and accessories provided with the service are unable to be customized. All devices and accessories are provided with standard branding, specification, and color combinations. Application deployment and policy configurations are handled through IT-as-a-Service.
- Data Recovery: User and team data, including personalization, is stored in OneDrive for Business, with only cache data residing locally. If data is intentionally stored on the device’s internal storage system, any data recovery must be attempted and completed prior to returning the device to Microsoft.
- Device Setup: Devices are delivered to the customer address, where they need to be powered on and set up by the customer.
Device Configuration:
Default Policy:
- Security baseline
- MMD recommended Security templates
- Update deployment
- Metered connection
- Device compliance
Diagnostic Data:
Devices will be set to provide enhanced diagnostic data to Microsoft under a known commercial identifier. As part of MMD, IT admins can not change these settings.
Security addendum
In addition to the Standard MMD default policy, there are additional security policies for highly regulated industries.
- Security Monitoring
- Disabled Powershell V2
Security in MMD
- Device Security
- Antivirus: Microsoft Defender AV
- Full Volume Encryption: Microsoft BitLocker with built-in Trust Platform Module(TPM)
- Monitoring: Microsoft Defender Advanced Threat Protection (Microsoft Defender ATP)
- Operating system updates: latest security updates.
- Secure Device Configuration: Microsoft Security Baseline.
- Identity and Access Management(Identity and access management protects corporate assets and business-critical data.): Azure Active Directory (Azure AD)
- Biometric Authentication: Windows Hello
- Standard user permission: Windows Autopilot(是一组用于设置和预配置新设备以让它们可供高效使用的技术。 你还可以使用 Windows Autopilot 来重置、恢复设备并重新调整其用途。 此解决方案可以让 IT 部门通过轻松简单的流程,在几乎不需要管理基础结构的情况下实现上述目标.)
- Network security
- VPN: a modern VPN solution / Azure Active Directory App Proxy
- Information security
- Data recovery: Information stored in key folders on the device is backed up to OneDrive for Business
- Windows Information Protection: Windows Information Protection and Azure Information Protection.
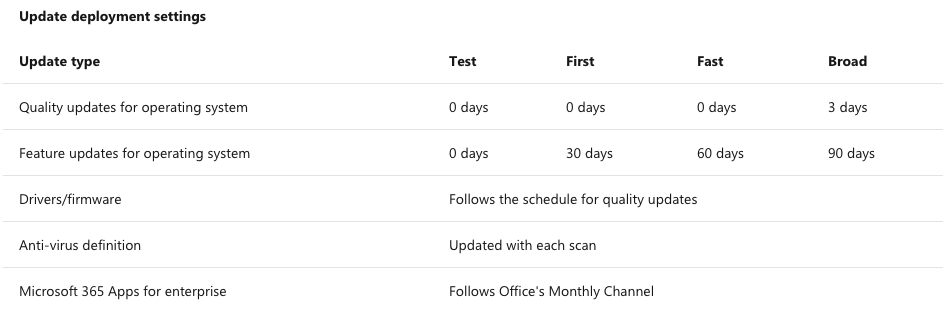
Updates:
MMD connects all devices to a modern cloud-based infrastructure. Keeping Windows, Office, drivers, firmware, and Microsoft Store for Business applications up to date is a balance of speed and stability. Deployment groups will be used to ensure operating system updates and policies are rolled out in a safe manner.
MMD uses four Azure AD groups to manage updates:
- Test
- First
- Fast
- Broad
Support
Microsoft will provide proactive and reactive incident management.
Customers can contact Microsoft Managed Desktop operations for:
- Information requests on the Microsoft Managed Desktop tenant or configuration
- Change requests to the configuration of Microsoft Managed Desktop devices
- Reporting an incident or outage
Microsoft Managed Desktop support includes:
- A team of engineers dedicated to MMD devices
- Support options for end users with MMD devices
- Grants limited administrative access to MMD devices for engineers managing MMD devices
Supported products:
- Windows 10 with Microsoft Defender Advanced Threat Protection (Microsoft Defender ATP)
- These Microsoft 365 Apps for enterprise apps: Outlook, Word, PowerPoint, Excel, Skype for Business client, Microsoft Teams
- Microsoft Store for Business
- OneDrive for Business client
Operations and monitoring
- Change process overview
- Before a change
- Set expectations for service changes. 2)Notify customers 5 days in advance for changes that require administrator action. 3) For emergency changes, apply a mitigation prior to notifying.
- Customer: 1) understand what to expect for changes and communications. 2) Read MMD Message center regularly. 3) Review and update internal change management processes. 4)Understand, and check compliance with MMD requirements. 5) Acknowledge and approve, when required.
- During a change
- Release and deploy monthly security and non-security updates for Windows 10 and Office 365 clients. 2) Monitor data signals and support queues for impact.
- Customer: 1) Check the MMD Message center and review any additional information. 2) Tack any action required, if applicable, and test applications. 3) If a break/fix scenario is experienced, create a support request.
- After a change
- Collect customer feedback to improve rollout of future changes. 2) Monitor data signals and support queues for impact.
- Customer: Work with people in your organization to adopt the change. 2) Review change and adoption management processes for opportunities to gain efficiencies. 3)Provide general feedback and specific feedback in the admin feedback tool. 4)Train users to provide app-specific feedback using the windows feedback hub and smole button in office apps.
- Before a change
- Standard operating procedures:
- Network(proxy,packet inspection,VPN)
- Advise and plan with customers to minimize risks to business users.
- Customer: Action1:Create a support request requesting information for a planned configuration change, including configuration details, scope, timeline and other pertinent details to review. Only apply a change once MMD Operations has assessed and advised.
- Service accounts
- Implement, securely store, and manage the credentials. Communicate unauthorized access or use of these credentials to your security operations team.
- Customer: in addition to Action1, Not ass policy,multi-factor authentication, conditional access, or application deployment to the MMD service Accounts. Not reset the password or use the credentials. Open a Sev C support request to MMD Operations if suspicious activity is observed in Intune or Azure audit logs, related to these service accounts.
- Device Groups
- Implement and manage the membership of devices within MMD groups. Use the MMD groups to manage the assignment and release of configuration and updates to devices.
- Customer: In addition to Action1, Not modify the membership of and MMD group. Only use the groups to assign corporate certificates for services such as VPN, Windows Hello for Business or email encryption, or corporate WiFi profile configuration. Where co-management exists, explicitly exclude all MMD groups when deploying the Configuration Manager client.
- Policies
- Implement and manage the MMD policies that govern the configuration state of devices within service. Deploy updates, to policy or Windows, incrementally using Device groups. Explicitly exclude targeting non-MMD group.
- Customer: In addition to action1, Not edit or assign MMD policies to devices or users not managed by the MMD service.
- Microsoft Defender Advanced Threat Protection
- Monitor and investigate devices within the scope of the MMD service.
- Customer: Same as action 1.
- Microsoft Store for Business
- Configure and maintain the windows. Autopilot profile for the MMD service.
- Customer: In addition to Action1, Not modify the configuration of the MMD windows Autopilot profile or add/remove assigned devices.
- Certificates
- Customer: Create a support request 60 days prior to a certificate expiring, requesting information for a planned configuration chgne, including confiugration details, scope, timeline and other pertinent details to review. Only apply a change once MMD operations has assessed and advised. Update all certificates that are required to configure certificate profiles, VPN profiles, and WiFi profiles.
- Network(proxy,packet inspection,VPN)
- Device wipe with factory reset
- The MMD Operations team can perform a factory reset of devices enrolled in the service when required. This is helpful if you need to give a device to a different employee, or if an employee leaves your company.
Application & Driver requirement
- Centrally managed apps and drivers. All applications and drivers installed on MMD must be deployed through Microsoft Intune, the Microsoft Store, or the Microsoft Store for Business; if available, drivers will also be deployed through the Windows Update service.
- Prohibited app classes
- 3rd party anti-virus, security, or audit software
- Versions of Microsoft Office prior to Microsoft 365 Apps for enterprise
- Applications that install or bundle other 3rd party software
- Driver Deployment:
- MMD only supports device drivers that are available through Windows Update or installed inbox with the Microsoft Managed Device.
- Restricted app behaviors:
- User Experience:
- Install background services
- Add itself to the Windows startup path
- Applications dependent on drivers
- 3rd party web browsers
- Security:
- Elevate the end user’s privileges
- Act as an app store or have a built-in extension manager
- Have known security vulnerabilities
- Encrypt or restrict access to end-user data
- Is unsigned or is signed using a certificate which doesn’t roll up to a trusted root
- User Experience: